The New Text Message Scam
Have you realized there’s a serious lack of emails in your inbox from Nigerian princes claiming you’ve magically inherited $7,285,51, but all you need to do is pay the processing fees to get the money? That’s no shock as everyone knows of those scams by now, even Grandma. If scammers are going to pull one over on you, they’re going to have to change up their tactics. And, they have.
The essence of a good scam is rooted in a couple of things. You want the victim to feel a sense of entitlement, you want them to feel a sense of reward, and you want to promise them
The latest scam revolves around a little social engineering to get you to reveal your 2FA keys. It’s actually pretty brilliant, and sadly I can see a lot of people falling prey as it’s so simplistic. Any good scam is at it’s core, and this one is incredibly well designed. Here’s how it goes down.
Your Passwords Is Weak. They’re Exploiting You.
If you don’t know by now, your passwords have been leaked to the open Internet. Possibly because you left yourself vulnerable and got completely pwned, but almost certainly because a website you’ve got an account with got compromised. This means that their entire user list is exposed, and in that list is likely millions of accounts, along with their associated email addresses, real names, addresses, and passwords. While the passwords aren’t in cleartext (meaning, they are easily read), they’re (hopefully) encrypted in some way. The thing is, with enough time and computing power hackers can easily decrypt your passwords back to cleartext without a whole lot of problem. If your password is within the list of the 1,000,000 most used, it can be cracked in a matter of a couple minutes on a semi-decent computer.
However, if you’re smart you rotate your passwords fairly often, never use the same password twice (use a password manager, people!), and your password is 16+ characters, with upper/lower, numbers, and special characters. This type of password will take years to crack using beefy servers. Plus, if someone came across a password like that, they’d completely bypass it as it’d prevent them from cracking the low hanging fruit. All of those things will provide a major first line of defense, but it’s not enough. You should also be using 2FA or “two factor authentication”. This mean that once you login to an account, you need to enter a secondary verification. This typically comes from a text message, email, or through an authenticator app such as Google Authenticator. Anyone who has your password would (probably) not have access to your secondary device to confirm the login, and that’s where this scam comes into play.
You’re Targeted Before It Begins.
These people aren’t just carpet bombing these messages to anyone. They have targeted you because they have your username and password. This has most likely come from some sort of data breach, and they have your access credentials into your email, social media, or whatever. They don’t however have access to your phone to get the 2FA text message. That’s where they target you.
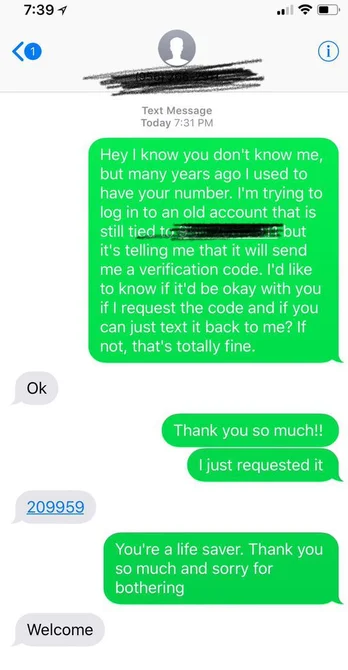
It’s really quite simple to pull off. You just ask the person to give you the code that gets sent to their phone. People are inherently ignorant and fairly stupid. Don’t oversell it, just give them a realistic scenario where they can “help”, and most will be happy to comply. Just look at the example here. All you need to do is come up with a quick story, they’ll be happy to help, and blamo, you’re in. They “request” the code by signing into YOUR account, where-as now you’ve just given them your backup key to your digital castle.
What they do from there is anyone’s best guess. Reset your password and lock you out? Scour for anything valuable that they can further exploit? Use your email to gain access to other accounts and reset their passwords? Steal your identity? Blackmail you with possible information or files they find? It could go on and on really. Each of these “hackers” has a different agenda in mind, but it’s all nefarious.
You’d think that most people wouldn’t be so quick to give up the secrets, but you need to remember that hundreds of thousands of people believed that they were somehow related to some rich Nigerian prince that had died and they were the last remaining survivor in their family so they’ll get 10’s of Millions if they only pay the “brokerage” fees. How many of you believed that if you forwarded “this email within 10 minutes” some company would track the email and you’d get paid like $10/person you sent it to?
So, maybe you’re keen and you tell them no. Surely any good social engineer will keep the conversation going, maybe send you some screenshots, anything to make it more believable. Most people will cave sooner or later, and a lot of those people consider themselves to be pretty smart and not susceptible to scams.
It May Come From Other Places.
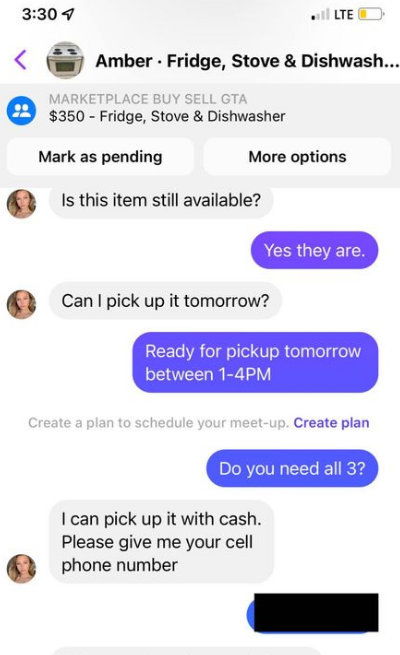
The new method is to track people down on social media. They’ll talk to you about something you’re selling, or find some other way to inject the idea they need your phone number for something, possibly to “verify” you’re real or “for their protection”. It’ll most likely be a an account of a fairly good looking woman, or a “mom”. They’re playing on the idea that they look trustworthy, or just straight up horny and you’re just happy to be selling your old couch to some magazine cover looking 24 year old college girl.
If it was me pulling the scam, I’d say “I’ve had some creepy people in the past, so I need to make sure it’s your phone number for my safety. I can do that by sending you a code and you tell it back to me to verify”. Who isn’t going to want to comply with the wishes of a woman to “make sure she’s safe” is the idea.
In another example, this is a Facebook message. Super simple attack once again. You may even find they’ll offer you an extra 25% just to “hold it until they can get there tomorrow” or something. An offer almost too good to be true, especially if they item has been listed for sale for quite some time, meaning you’re probably super excited to get rid of it.
Heck, it could even be a super attractive person who’s hitting on you slowly but surely and then they ask for your number so you can start texting later or whatever. This isn’t as clever as there’d be less reason for them to “verify” your phone number per-say, but if someone really wants to social engineer you, they will. Sometimes the long game is far more effective when you’re dealing with someone particularly prudent when it comes to these things.
How To Fight Back
I’m the kind of guy who likes to mess with scammers if not for my own mental masturbation. I deal with duct cleaning calls by telling them I’m excited for the service, then sending them to Doug Ford’s house. About half the time they call and say nobody is answering the door or they can’t get in the driveway. I waste their time. Granted, all I’m doing is wasting the time of some poor contractor that bought leads from scammers, but if they get enough of this they’ll stop buying those leads and those scammers will have one less customer.
So, how to deal with this scam? Simply tell them that you’ll help them. After all, YOU are the target here, so why not play into it? Tell the person asking for the secure code that while you understand it’s a scam, that you’ll help them. Ask them to provide you the username and password they used to get into the account and you’ll reset the password for them. After all, that’s exactly what you’re going to do – you’re not lying. What you’re literally asking them for is YOUR username and password.
Chances are they’ll deny it, or simply stop replying. Either way, you should be reporting the account this person contacted you from for fraud (on whatever platform it is), and also alerting other members of that group or whatever to the scam user. They’ll simply create another account and pull the same stuff, but it’s good to educate people as to the methods much like I’m doing here. You can link to this blog post if you’d really like.
But, you need to follow through. Login to your account and reset your password. You see, this whole scam revolves around the idea that your username and password have been leaked somehow, so just change the password and you’re back to having a more secure account. If they somehow cough up the account name or website, you know which account of yours has been compromised. Social engineer them a little bit and say something like “Oh, sure! Which website is it for?”. They may retort and say “you should have the code”, completely glassing over your question. You reply “I got 2 codes, one for [Gmail/Hotmail/Outlook – whatever your email provider is], and one that doesn’t specify. Which one is it?”. That’ll trick them into revealing if it’s your email password or not. You can even go so far as to request they tell you “for security so you don’t give them the wrong one”, and they’re going to have to agree before you “help” them. Just outplay them at their own game.
At the end of the day, the point is to NEVER give out any “code” that is EVER sent to you. From ANYONE. This goes for any unsolicited call, message, email, whatever. Never give your code, never give access, and never just agree to things even if they seem logical. If you are SERIOUSLY doubting something may be real, and the person represents a company like “It’s David from Google and we need to verify your account”, or “This is Jeff from Mastercard and we need….”, then you tell them that you’ll call the company back. You do so using the phone number that is provided to you FROM THE COMPANY, and NEVER the phone number that they provide you or what comes up on your call display. In the end, no company will ever call you like this, nobody needs to verify anything, and it’s all just one elaborate scam to rip you off and make your life miserable. Don’t fall for it.
Obligatory “Work” Picture
Here’s Some Food
Categories
- Ramblings (26)
- Life (9)
- Nerd Stuff (5)
- Rants (9)
- Shower Thoughts (3)
- Recipes (6)
Tags
What Ya'll Like...
- Let’s Make Some Stock 224 views | posted on April 11, 2024
- So, I Guess I Quit DJing. 217 views | posted on March 9, 2022
- The Future Of NHL Hockey Broadcasts 157 views | posted on May 18, 2024
- Chicken with Mushroom Cream Sauce, Sprouts & Parsnips 152 views | posted on October 7, 2021
- I Just Spent $160 On A Toothbrush 138 views | posted on August 8, 2023
What Ya'll Think...
© Paul Hattlmann. All rights reserved.
Powered by pasha.solutions - Bless OpenSource
All opinions, posts, comments, & content are solely that of my own. They in no way, implied or otherwise, represent the views or opinions of any business, corporation, or entity that I may be associated with.


Leave a Reply